Oct 9, 2013 | HowTo, Technology
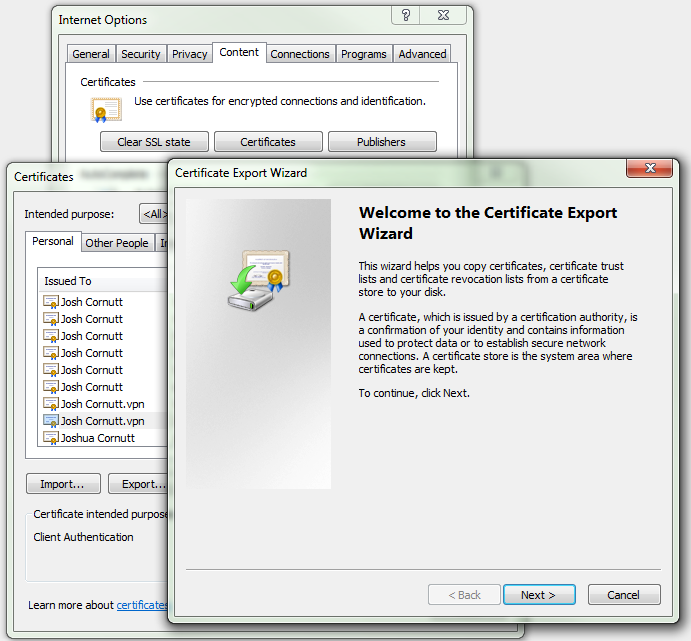
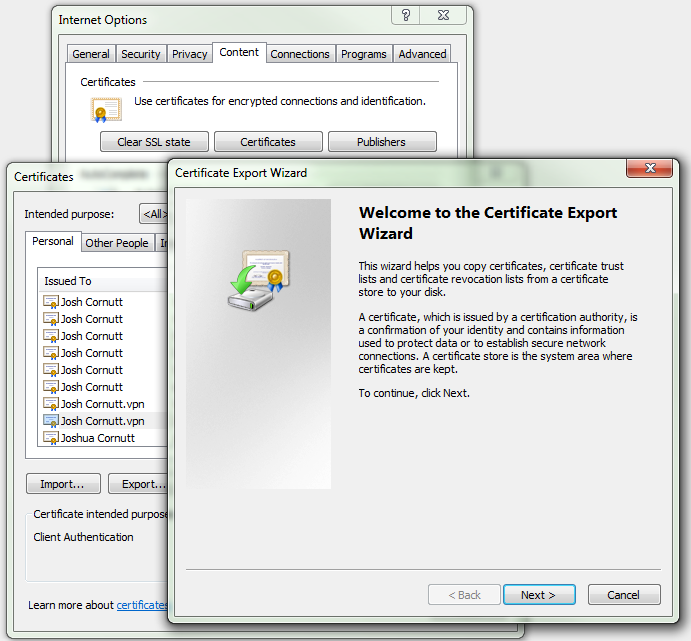
If you have a PKI certificate in your Windows PC that you would like to use to log in to your OpenSSH-enabled Linux server, it can be a pain to figure out how to extract the public key from this file and convert it into a format OpenSSH can understand.

Sep 3, 2013 | General Articles, Technology, WWPass related
As professionals in the authentication space, we stay up to date with technology providers and their solutions. For this post I have invited Abby Porter, Director of Product Management at Delfigo Security to discuss whether it’s time to get rid of passwords all together, and the challenges associated with doing so.

Aug 8, 2013 | General Articles, Reviews, Technology
The Dyn Geek Summer Camp 2013 conference in Manchester, NH was held yesterday and today. It was probably the best conference I’ve been to this year and, best of all, it was a 5 minute walk from work. Great speakers, great entertainment, a great facility, and great food! This was Dyn’s first year hosting this conference and I hope they continue this new tradition as it was a blast and I felt like I’m walking away with a little more insight into what’s to come in the realm of technology. Here’s some photos and videos!

Aug 3, 2013 | HowTo, Technology
If you believe your computer may be experiencing hard drive failure or if you would just like to make sure the hard drive you use to store all of your data currently is in good shape, you should test your hard drive for errors! There are many free utilities out there that perform some basic tests or read the S.M.A.R.T. data, but it’s hard to beat a utility made by one of the largest hard drive manufacturers, Seagate (I mean, c’mon, who knows hard drives better than those that create them).

Jul 23, 2013 | Technology
There are two types of software companies; those that profit from improving the user’s experience and those that profit from the user’s lack of technical knowledge. When designing software, it’s easy to take the lazy route and only create the bare minimum required to make a process work (requiring manual editing of configuration files, setting permissions, offloading any other unfinished task to the end-user). Even if the software being created does, in the end, accomplish a complex task, the result will be an alienated customer with dwindling chance of any purchase in the future.