Your Password Manager Is Insecure
Unfortunately, not every website on the internet takes security all that seriously and still requires users to sign-up and authenticate with usernames and passwords. More progressive websites have started to allow users to log-in with their existing passwords but tack on a “second factor” authentication such as an SMS/text message code being sent to your phone or an e-mail with a One-Time Password (OTP). Inversely, Password Managers solve the problem of having to remember thousands of passwords to different websites but the security of these managers are typically sub-par and often require a single password (“master password”) to access your list of passwords. Talk about putting all of your eggs in one (very insecure) basket.
How To Secure Your Passwords
Public Key Infrastructure (PKI) digital certificates are the answer. The idea is that you will generate a secure (and lengthy)
private keyand use that key to encrypt another key and use that final key as your “password” to unlock your password manager. On top of that security, you should also be able to provide a password that you know to go with it. I will show you how to protect your KeePass password manager with true Two-Factor Authentication (2FA) using
something you haveand
something you know.
Getting Started
Download KeePass (if you’re not already using it)
[box type=”download”] If you don’t have KeePass already, you can download it from the
KeePass Download Page. Get the
Professional Edition. [/box]
Download the KeePass CertKeyProvider plugin
[box type=”download”] You can get the CertKeyProvider plugin from the
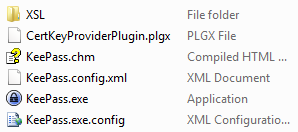
KeePass Plugin Download Page. [/box] Once you have downloaded the plugin, copy the PLGX file into your KeePass software directory (where your KeePass.exe is located).
Generate a PKI certificate
If you don’t already have a certificate to use you can generate one using OpenSSL. I outline the steps of creating a new certificate in another article;
Securing OpenSSH with WWPass PassKeyin Step #1. If you already have a digital certificate (preferably loaded on a Smartcard) then you can skip this step.
Configure KeePass Security
- Launch KeePass to get started. Create a new database (File->New) and tell KeePass where to place this new database.
- You should now see the Create Composite Master Key page. Here you should specify a Master Password and change the Key file / provider to Certificate-protected key.
- Choose a place to save your encrypted key file (which can only be “unlocked” using your password and certificate).
- Select a certificate to use to protect your key file.
Conclusion
You’ve now set up a KeePass database that can only be opened if you provide a correct password and also a digital certificate. Quick and dirty Two-Factor Authentication for your list of passwords. If you need more security you should consider storing your certificates within a secure platform such as a Smartcard or the
WWPass PassKey. These allow you to create a private key or import an existing one but from then on your private key will never leave the device again. This is considered an “unextractable” key and is a considerable increase in security as your private key can no longer be stolen through software (viruses, malware, etc…) or physical theft.

Leave a Reply
You must be logged in to post a comment.